Security and Compliance, Simplified.
Managed Security that Extends Beyond Automation
ArmorPoint Managed SIEM combines network visibility, event correlation, and threat intelligence with the delivery of ongoing managed services that surpasses the automation delivered by SIEM tools and the capabilities of your in-house resources.
ArmorPoint USM Pricing
ArmorPoint
Managed SIEM Pricing
Core
MONITORING AND
REPORTING
Starting at $250
Per Month
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Analyze
MANAGED MONITORING
AND REPORTING
Starting at $500
Per Month
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Edge
MANAGED RESPONSE
TO NETWORK EDGE
Starting at $750
Per Month
FOR ORGANIZATIONS WITH
Some IT security staff
Managed services provider
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to Network Edge
- 10 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
360˚
MANAGED RESPONSE
TO THE ENDPOINT
Starting at $1,500
Per Month
FOR ORGANIZATIONS WITH
Little to no IT staff
Strict compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to the Endpoint
- 20 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
ArmorPoint Managed SIEM Pricing
Analyze
MANAGED MONITORING
AND REPORTING
Starting at $500 Per Month
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Edge
MANAGED RESPONSE
TO NETWORK EDGE
Starting at $750 Per Month
FOR ORGANIZATIONS WITH
Some IT security staff
Managed services provider
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to Network Edge
- 10 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
360˚
MANAGED RESPONSE
TO THE ENDPOINT
Starting at $1,500 Per Month
FOR ORGANIZATIONS WITH
Little to no IT staff
Strict compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to the Endpoint
- 20 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
ArmorPoint Unified Security Management (USM) Pricing
Core
MONITORING AND REPORTING
Starting at $250 Per Month
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Full-stack Detection and Response
ArmorPoint provides the security data collection of a SIEM coupled with the expertise of managed security services, eliminating the need to buy expensive hardware or hire more staff.
Speed and skill are of the essence when defending your data assets against attack. Knowing what needs attention and what is simply “noise” requires training and a dedicated team to properly triage events for efficient and effective resolution.
When a security event occurs, ArmorPoint agents will quickly investigate to determine the severity of the attack and correlate it with other events. Our experienced, highly trained security engineers will notify you of the severity of the attack, the relevance to the security environment, and the threat to your business services.
When validated security events are detected through ArmorPoint’s two-step verification process, the response efforts must begin without delay. ArmorPoint agents initiate the response process, collect the pertinent data, provide updated incident reports, and remediates the threat.
Triaging and reporting on the most severe events doesn’t mean you should ignore the “lesser” alerts. ArmorPoint will review and analyze all alert data for hidden malicious activity, and recommend the best path forward. We provide regular reports for your team to review as part of the monitoring and environment oversight process.
Proactive Expert-level Security
To get the most value from your SIEM solution, you need a security partner who will give you help when and where it matters most.
Resolve potential incidents automatically with built-in scripts designed to detect, mitigate, and eliminate threats.
As cyber threats and hackers grow faster and more agile, ArmorPoint combines evasion resistant CPU-level detection and OS-level sandboxing to rapidly identify exploits before they can cause critical damage to your company network.
ArmorPoint threat hunters stay up-to-date and trained in the forever-evolving black-hat world of hacking techniques, tools, and other malicious exploits to transform real threat data into actionable intelligence.
Streamline Compliance Management
Pre-defined reports support a wide range of compliance auditing and management needs, including PCI-DSS, HIPAA, SOX, NERC, FISMA, ISO, GLBA, GPG13, and SANS Critical Controls.
Quickly know where your organization stands when you’re ready to meet or maintain industry-mandated compliances.
Continually assess and easily prove compliance with regulations with real-time infrastructure mapping and full-stack topology.
Understand the Risk of Valid Threats
Using data gathered from continually scanning and monitoring your organization’s environment, ArmorPoint analyzes, validates, and alerts key stakeholders of cyber threats and areas of exploit, providing the critical data and analytics needed to appropriately strategize and realign ongoing security efforts.
When ArmorPoint validates a cyber threat, it’s assigned a risk level that correlates to how the threat could affect critical business functions.
Predefined correlation rules as well as more advanced machine learning help identify insider and incoming threats that pass traditional defenses. High fidelity alerts raise the profile of high-priority actions identified within the organization.
ArmorPoint analysts deliver an in-depth report detailing the root cause analysis of all verified incidents and uses the findings to review and redefine current practices to give your company the security and flexibility needed to quickly detect, protect, and effectively respond to security threats before they even start.
Gather and Infuse Security Intelligence
The integration of external threat intelligence feeds gathers the data needed to keep you safe from malicious activity throughout global threat landscape, rapidly identify root causes of threats, and take the steps necessary to remediate and prevent them in the future.
Over three million sensors deployed around the world provide early warning of activity in the global cyber space, giving ArmorPoint the indicators of compromise needed to proactively protect your organization from emerging threats.
Should an indicator of compromise be detected within your organization’s environment, ArmorPoint automatically implements safeguards to protect from destructive malware, botnets, mobile, and zero-day vulnerabilities.
As cyber criminals develop new ways to attack, ArmorPoint automatically detects new exposures against previously remediated issues.
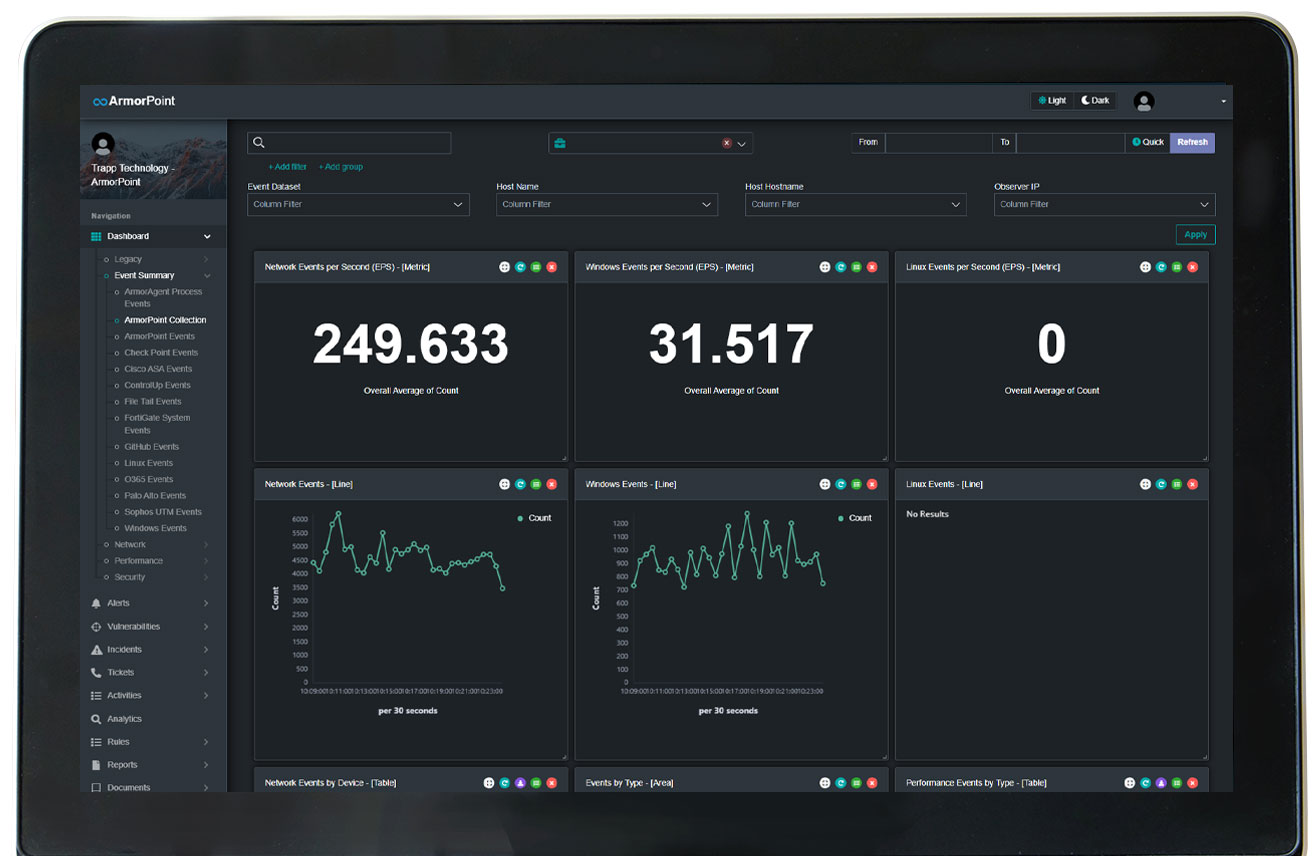
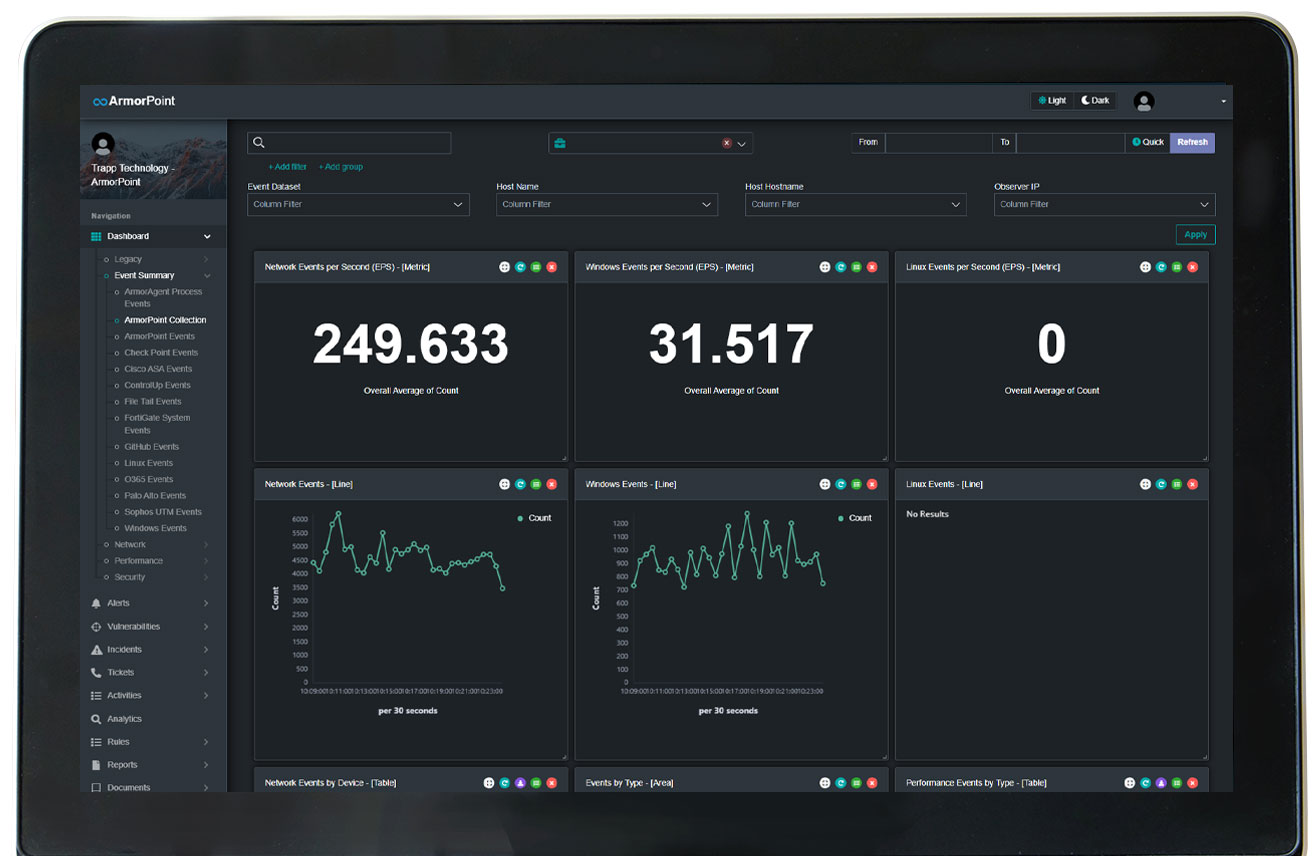
Pulse-Check with Advanced Analytics
View and share the data that matters to you most with access to dynamic dashboards, reports, and analytics from across the organization.
View the current status of your environment in real-time with customizable KPI dashboards that display the data you need to make decisions.
Easily schedule and deliver relevant reports to key business stakeholders.
View all of your assets through a single pane of glass through an up-to-date Centralized Management Database, which enables sophisticated context-aware event analytics.
Free Up Internal Teams
Leave the 24/7/365 monitoring, analysis, and remediation efforts to ArmorPoint cyber security professionals and free up time for overburdened IT teams that often handle IT support, security, and even compliance.
Avoid ending up with “shelfware” and experience faster implementation times and less operational bottlenecks with ArmorPoint’s fully managed SIEM deployment.
Rather than struggling to juggle business innovation and operational excellence requirements, internal teams are made available to refocus on revenue-generating projects while retaining control of the organization’s security monitoring capabilities.
Only 19 percent of IT leaders say they report all data breaches to the CEO and board of directors. ArmorPoint creates a clear view for business leaders through managed reporting, absolving IT leadership from the duty of incident notification, and creating availability for them to focus on security strategy and related initiatives.
Fill the Gaps in Security Management
Whether you have an IT team of one or one hundred, find the level of service that keeps your organization operating at peak performance.
The deep bench of ArmorPoint security experts and analysts continually monitor and evaluate your environment, 24/7/365.
With ArmorPoint’s remote incident response services, our U.S.-based team of certified threat hunters, analysts, and engineers defend your organization from any geophysical location.
On select plans, the team of ArmorPoint threat hunters will identify, block, and remediate active threats within the network down to the endpoint.
ArmorPoint Plans
ArmorPoint is a two-part security solution, comprised of a level of security and a level of service that reduces your costs while maximizing value.
Analyze
MONITORING AND
REPORTING
![]()
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
LEVEL OF SECURITY
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
LEVEL OF SERVICE
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Edge
MANAGED RESPONSE TO
NETWORK EDGE
![]()
FOR ORGANIZATIONS WITH
Some IT security staff
Managed services provider
LEVEL OF SECURITY
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
LEVEL OF SERVICE
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to Network Edge
- 10 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
360˚
MANAGED RESPONSE TO
THE ENDPOINT
![]()
FOR ORGANIZATIONS WITH
Little to no IT staff
Strict compliance requirements
LEVEL OF SECURITY
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
LEVEL OF SERVICE
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to the Endpoint
- 20 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
Advanced Agent Monitoring Required for the Following Security Features:
• Performance Monitoring
• Availability Monitoring
• Real-time Configuration Change Monitoring
• Rich Customizable Dashboards
• Out-Of-The-Box Compliance Reports
• API-based External Technology Integrations
• Two-factor Authentication
VERSION: MOBILE & TABLET PORTRAIT
Security and Compliance, Simplified.
Managed Security that Extends Beyond Automation
ArmorPoint combines network visibility, event correlation, and threat intelligence with the delivery of ongoing managed services that surpasses the automation delivered by SIEM tools and the capabilities of your in-house resources.
Core
MONITORING AND
REPORTING
Starting at $250 Per Month
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Analyze
MANAGED MONITORING
AND REPORTING
Starting at $500 Per Month
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
CLICK TO COMPARE!
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Edge
MANAGED RESPONSE TO
NETWORK EDGE
Starting at $750 Per Month
FOR ORGANIZATIONS WITH
Some IT security staff
Managed services provider
CLICK TO COMPARE!
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to Network Edge
- 10 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to Network Edge
- 10 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
360˚
MANAGED RESPONSE TO
THE ENDPOINT
Starting at $1,500 Per Month
FOR ORGANIZATIONS WITH
Little to no IT staff
Strict compliance requirements
CLICK TO COMPARE!
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to the Endpoint
- 20 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to the Endpoint
- 20 Hours of Remote Incident Response Services per Month
- Root Cause Analysis

Full-stack Detection and Response
ArmorPoint provides the security data collection of a SIEM coupled with the expertise of managed security services, eliminating the need to buy expensive hardware or hire more staff.
Speed and skill are of the essence when defending your data assets against attack. Knowing what needs attention and what is simply “noise” requires training and a dedicated team to properly triage events for efficient and effective resolution.
When a security event occurs, ArmorPoint agents will quickly investigate to determine the severity of the attack and correlate it with other events. Our experienced, highly trained security engineers will notify you of the severity of the attack, the relevance to the security environment, and the threat to your business services.
When validated security events are detected through ArmorPoint’s two-step verification process, the response efforts must begin without delay. ArmorPoint agents initiate the response process, collect the pertinent data, provide updated incident reports, and remediates the threat.
Triaging and reporting on the most severe events doesn’t mean you should ignore the “lesser” alerts. ArmorPoint will review and analyze all alert data for hidden malicious activity, and recommend the best path forward. We provide regular reports for your team to review as part of the monitoring and environment oversight process.

Proactive Expert-level Security
To get the most value from your SIEM solution, you need a security partner who will give you help when and where it matters most.
Resolve potential incidents automatically with built-in scripts designed to detect, mitigate, and eliminate threats.
As cyber threats and hackers grow faster and more agile, ArmorPoint combines evasion resistant CPU-level detection and OS-level sandboxing to rapidly identify exploits before they can cause critical damage to your company network.
ArmorPoint threat hunters stay up-to-date and trained in the forever-evolving black-hat world of hacking techniques, tools, and other malicious exploits to transform real threat data into actionable intelligence.

Streamline Compliance Management
Pre-defined reports support a wide range of compliance auditing and management needs, including PCI-DSS, HIPAA, SOX, NERC, FISMA, ISO, GLBA, GPG13, and SANS Critical Controls.
Quickly know where your organization stands when you’re ready to meet or maintain industry-mandated compliances.
Continually assess and easily prove compliance with regulations with real-time infrastructure mapping and full-stack topology.

Understand the Risk of Valid Threats
Using data gathered from continually scanning and monitoring your organization’s environment, ArmorPoint analyzes, validates, and alerts key stakeholders of cyber threats and areas of exploit, providing the critical data and analytics needed to appropriately strategize and realign ongoing security efforts.
When ArmorPoint validates a cyber threat, it’s assigned a risk level that correlates to how the threat could affect critical business functions.
Predefined correlation rules as well as more advanced machine learning help identify insider and incoming threats that pass traditional defenses. High fidelity alerts raise the profile of high-priority actions identified within the organization.
ArmorPoint analysts deliver an in-depth report detailing the root cause analysis of all verified incidents and uses the findings to review and redefine current practices to give your company the security and flexibility needed to quickly detect, protect, and effectively respond to security threats before they even start.

Gather and Infuse Security Intelligence
The integration of external threat intelligence feeds gathers the data needed to keep you safe from malicious activity throughout global threat landscape, rapidly identify root causes of threats, and take the steps necessary to remediate and prevent them in the future.
Over three million sensors deployed around the world provide early warning of activity in the global cyber space, giving ArmorPoint the indicators of compromise needed to proactively protect your organization from emerging threats.
Should an indicator of compromise be detected within your organization’s environment, ArmorPoint automatically implements safeguards to protect from destructive malware, botnets, mobile, and zero-day vulnerabilities.
As cyber criminals develop new ways to attack, ArmorPoint automatically detects new exposures against previously remediated issues.
Pulse-Check with Advanced Analytics
View and share the data that matters to you most with access to dynamic dashboards, reports, and analytics from across the organization.
View the current status of your environment in real-time with customizable KPI dashboards that display the data you need to make decisions.
Easily schedule and deliver relevant reports to key business stakeholders.
View all of your assets through a single pane of glass through an up-to-date Centralized Management Database, which enables sophisticated context-aware event analytics.

Free Up Internal Teams
Leave the 24/7/365 monitoring, analysis, and remediation efforts to ArmorPoint cyber security professionals and free up time for overburdened IT teams that often handle IT support, security, and even compliance.
Avoid ending up with “shelfware” and experience faster implementation times and less operational bottlenecks with ArmorPoint’s fully managed SIEM deployment.
Rather than struggling to juggle business innovation and operational excellence requirements, internal teams are made available to refocus on revenue-generating projects while retaining control of the organization’s security monitoring capabilities.
Only 19 percent of IT leaders say they report all data breaches to the CEO and board of directors. ArmorPoint creates a clear view for business leaders through managed reporting, absolving IT leadership from the duty of incident notification, and creating availability for them to focus on security strategy and related initiatives.

Fill the Gaps in Security Management
Whether you have an IT team of one or one hundred, find the level of service that keeps your organization operating at peak performance.
The deep bench of ArmorPoint security experts and analysts continually monitor and evaluate your environment, 24/7/365.
With ArmorPoint’s remote incident response services, our U.S.-based team of certified threat hunters, analysts, and engineers defend your organization from any geophysical location.
On select plans, the team of ArmorPoint threat hunters will identify, block, and remediate active threats within the network down to the endpoint.
ArmorPoint Plans
ArmorPoint is a two-part security solution, comprised of a level of security and a level of service that reduces your costs while maximizing value.
Analyze
MONITORING AND
REPORTING
![]()
FOR ORGANIZATIONS WITH
Dedicated IT security staff
Minimal compliance requirements
LEVEL OF SECURITY
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
LEVEL OF SERVICE
- Basic Reporting
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Recommendations
Edge
MANAGED RESPONSE TO
NETWORK EDGE
![]()
FOR ORGANIZATIONS WITH
Some IT security staff
Managed services provider
LEVEL OF SECURITY
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
LEVEL OF SERVICE
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to Network Edge
- 10 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
360˚
MANAGED RESPONSE TO
THE ENDPOINT
![]()
FOR ORGANIZATIONS WITH
Little to no IT staff
Strict compliance requirements
LEVEL OF SECURITY
- 24/7/365 Monitoring
- NOC and SOC Analytics
- Real-time Asset Discovery
- Distributed Event Correlation
- Dashboards
- User and Entity Behavior Analysis
- Threat Intelligence Integration
LEVEL OF SERVICE
- Customized Reporting
- Automated Incident Management
- Human Analysis of Events
- Incident Notification SLA
- Incident History
- Remediation Planning
- Threat Remediation to the Endpoint
- 20 Hours of Remote Incident Response Services per Month
- Root Cause Analysis
Advanced Agent Monitoring Required for the Following Security Features:
• Performance Monitoring
• Availability Monitoring
• Real-time Configuration Change Monitoring
• Rich Customizable Dashboards
• Out-Of-The-Box Compliance Reports
• API-based External Technology Integrations
• Two-factor Authentication

